Malware: The Silent Infiltrator
Every digital system breathes data, streaming, syncing, backing up, restoring. It feels orderly, governed, safe. But in that endless rhythm, a poisoned file can slip through unnoticed. That’s how breaches begin — quietly, invisibly, long before any alert fires.
Picture this: a user uploads a harmless-looking ZIP file to your object store. Hidden inside is a new trojan, one not yet known to signature databases. The file lands, stored and replicated, waiting. Days later, a scheduled process executes it, encrypting files across nodes and corrupting replicas, the infection spreading deeper with every automated task. What began as a single upload has turned the storage cluster itself into the carrier. This could be a scenario that plays out most often at the edge or branch offices, where data is stored locally and security visibility is thinnest.
When the Invisible Becomes Inevitable
Malware has become the background radiation of the internet — constant, pervasive, and often unseen until it’s too late. In the past year alone, researchers identified over 100 million new malware strains, and 81% of organizations faced at least one malware incident. The real cost isn’t just downtime or cleanup, it is the erosion of confidence in data itself. Infection paths are endlessly inventive: dormant malware hiding inside archived data, compromised uploads introducing corrupted files, or insider misconfigurations allowing malicious code to spread within a storage cluster. These threats don’t outsmart defenses; they outwait them.
And the quietest, most dangerous place for them to hide is the storage layer. Storage is where everything ultimately rests: objects, snapshots, archives, replications. Once malware reaches that layer, traditional defenses offer little protection. You can patch a server, but you can’t patch corrupted data. One compromised file can evolve from a sleeping parasite into the root of a full-scale breach, infecting not just live data but every archived copy that trusts it.
Designing the Immune System Against Malware
Traditional defenses were built like walls meant to keep threats out. But data doesn’t stay behind walls anymore; it moves across clouds, edge/ROBO locations, APIs, and shared environments where malware can drift in through trusted paths. Modern defense demands evolution: systems with instincts, capable of detecting subtle anomalies and responding before infection spreads. In storage, that means proactive defense: continuous monitoring of both the system and the data it holds, always alert to what doesn’t look right. But vigilance alone isn’t enough. True cyber resilience depends on unified visibility and automated response: one intelligent layer that tracks every scan, threat, and event, and enforces policy the moment danger appears.
Bringing the Immune System to Life for Your Edge Data
Edge environments don’t have the luxury of layered security stacks or specialized teams. Remote offices, branch locations, and small IT setups need protection that works out of the box, and not another platform to integrate and manage.
Swarm Appliance is a turnkey, all-in-one object storage appliance designed to archive and protect local data at edge and ROBO sites, as well as SMB environments constrained by budget, space, and IT staff. It combines storage, data protection, and built-in malware detection in a single system that can be deployed quickly and operated with minimal overhead. Security isn’t bolted on or delegated to external tools; it’s embedded directly into how data is stored. By delivering intelligent malware defense as part of a self-contained system, Swarm Appliance reduces complexity while closing one of the most common security gaps at the edge — uninspected data quietly accumulating in local storage.
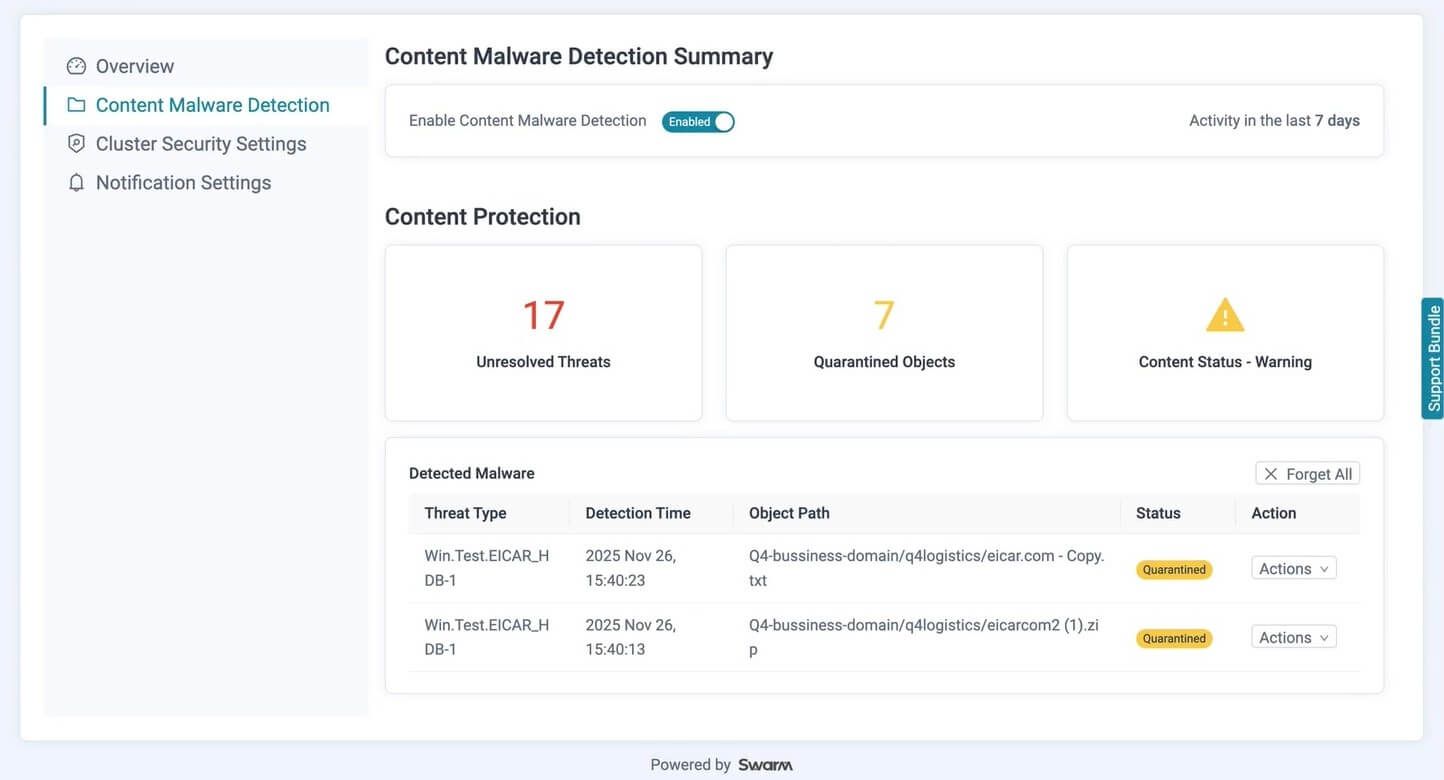
Content Malware Detection: Guarding Stored Data
Central to Swarm Appliance protection model is Content Malware Detection, designed to safeguard data the moment it is written to local object storage. Every time a user uploads content or an external system writes an object, the file can be automatically scanned for known malware signatures, trojans, and other malicious payloads.
This inspection happens after the data is stored, ensuring threats are identified before objects are replicated, archived, or consumed by downstream processes. By operating directly within the storage layer, malware detection works even when threats arrive through trusted paths or evade traditional perimeter defenses.
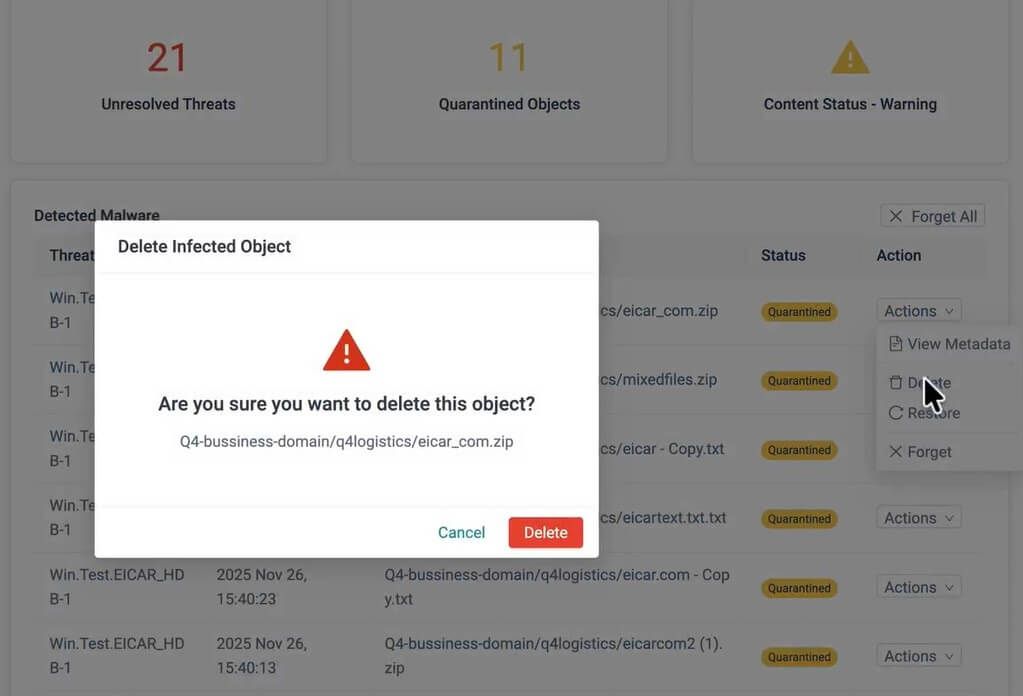
When malware is detected, administrators are notified and can take action based on their operational requirements. Infected objects can be reviewed and isolated in a secure quarantine bucket or removed entirely. Detection events include clear metadata such as threat type, source path, detection time, and status, enabling rapid review without forensic complexity.
For environments using Object Lock, regulatory and retention guarantees remain intact. Locked objects are not automatically quarantined or altered, preserving compliance while still providing visibility into detected threats.
By embedding malware detection directly into object storage, Swarm Appliance ensure that edge data remains trustworthy, and not just available.
Conclusion: Don’t Let Storage Be the Weak Link
Malware has become the quietest crisis in modern IT, hiding in files, lurking in archived objects, and waiting for the smallest lapse to resurface. It doesn’t just steal data; it corrupts the trust that data is built on. In that landscape, passive storage becomes risk storage. Modern object storage must do more than preserve information; it must defend it. With Swarm Appliance, DataCore brings real-time security awareness and response into the heart of object storage itself, ensuring malware threats are detected where they hide. Because when every file can be a weapon, security can’t live only on the perimeter anymore. To see how this new approach strengthens your environment, contact DataCore and experience the evolution firsthand.
